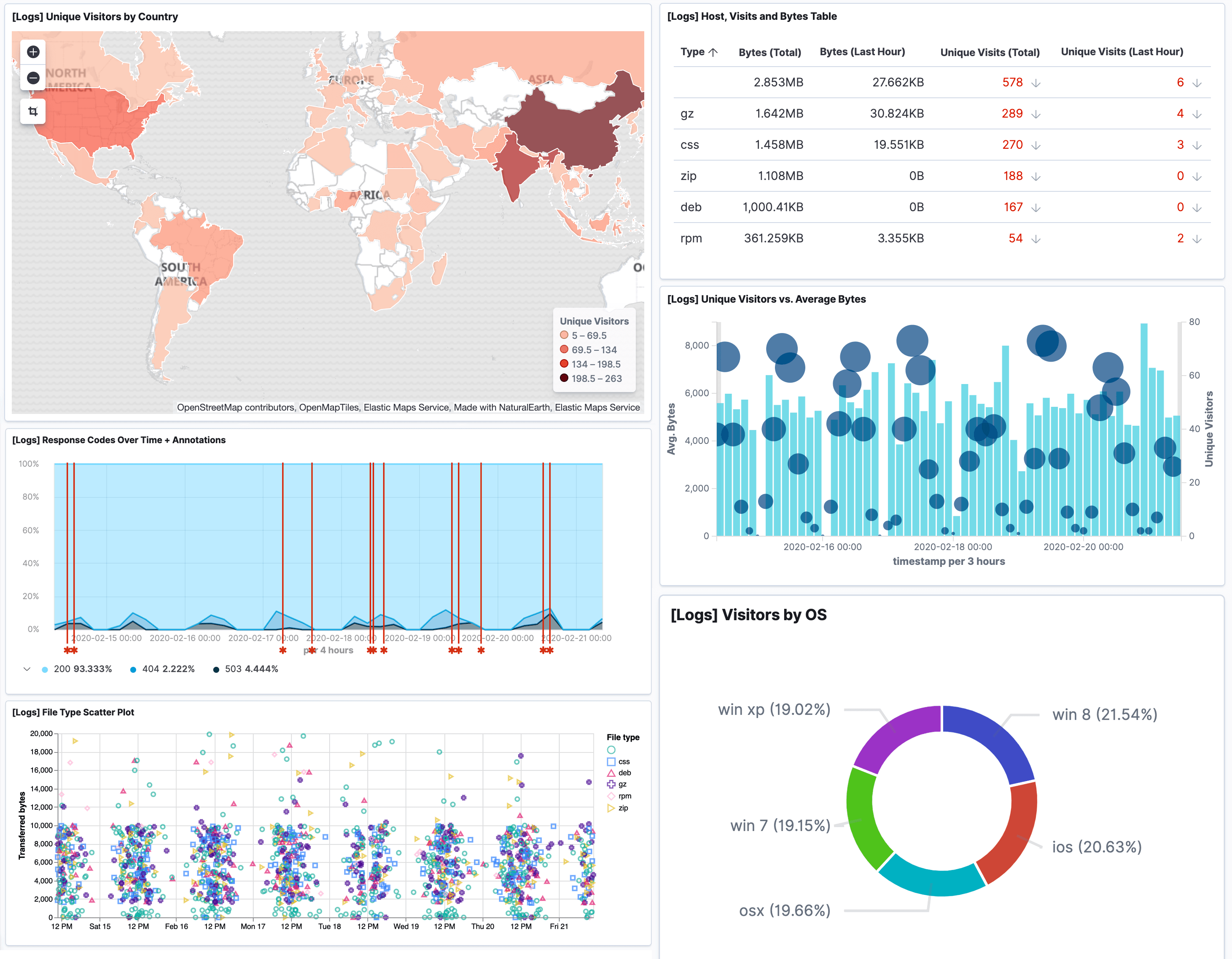
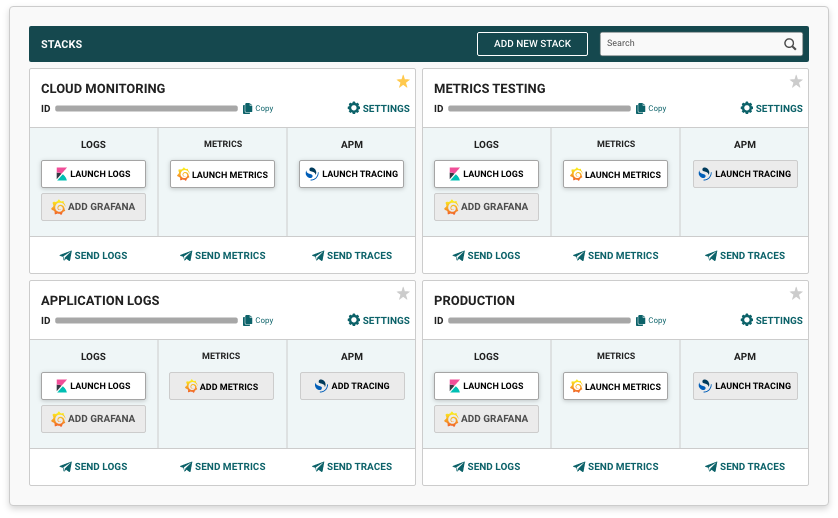
Accelerated Troubleshooting: Minimize mean time to resolution (MTTR) with comprehensive visibility into application behavior. Our platform provides the detailed context and powerful search capabilities needed to quickly identify root causes of application issues, reducing downtime and improving service reliability.
Performance Optimization: Identify performance bottlenecks and optimization opportunities through detailed application metrics and transaction monitoring. By analyzing response times, resource utilization, and code execution patterns, our platform helps you continuously improve application performance.
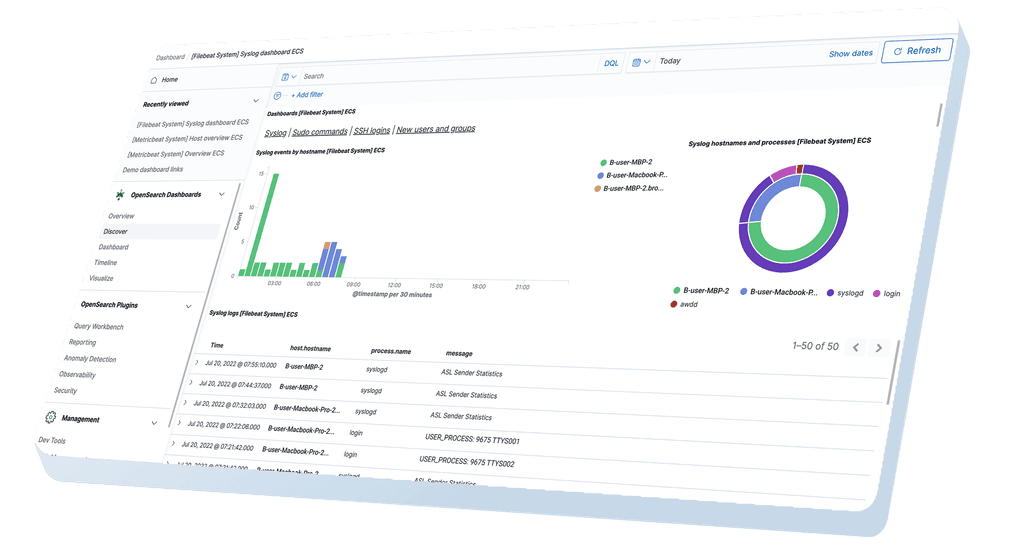
Enhanced Security Monitoring: Strengthen your security posture with comprehensive logging of authentication events, access patterns, and potential security anomalies. These detailed logs provide the foundation for effective security monitoring, incident response, and compliance verification.
Continuous Improvement: Support development excellence with insights derived from production application behavior. By analyzing real-world usage patterns, error frequencies, and performance metrics, your teams can make data-driven decisions about feature development, refactoring priorities, and technical debt remediation.