Why You Should Consider Compliance For Your SME
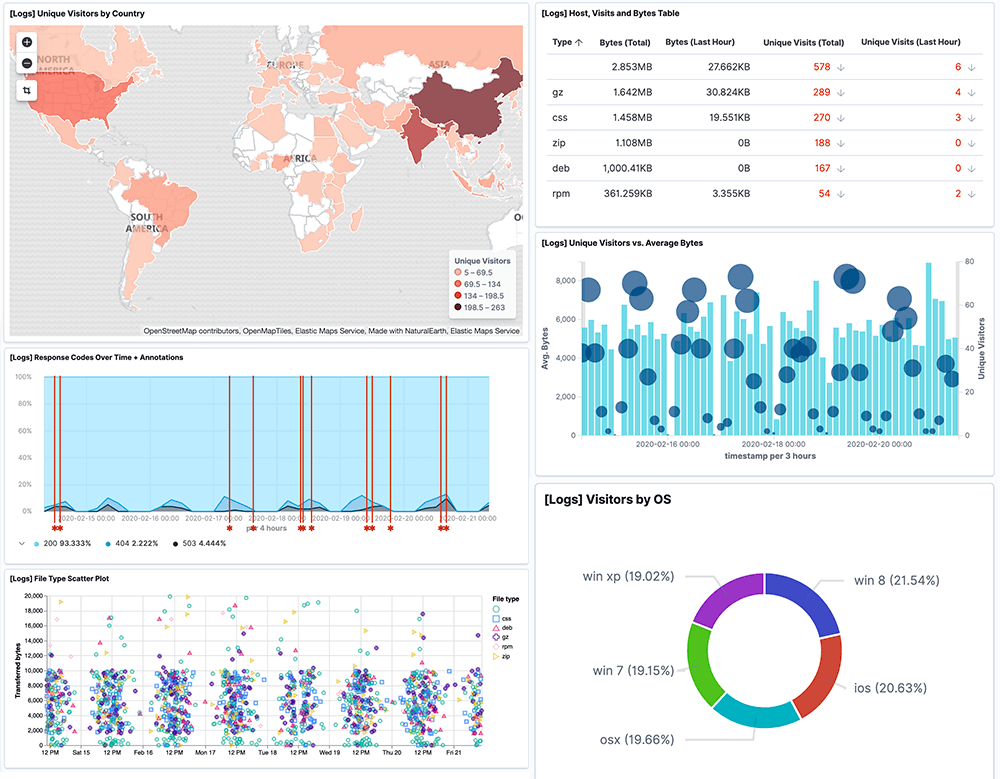
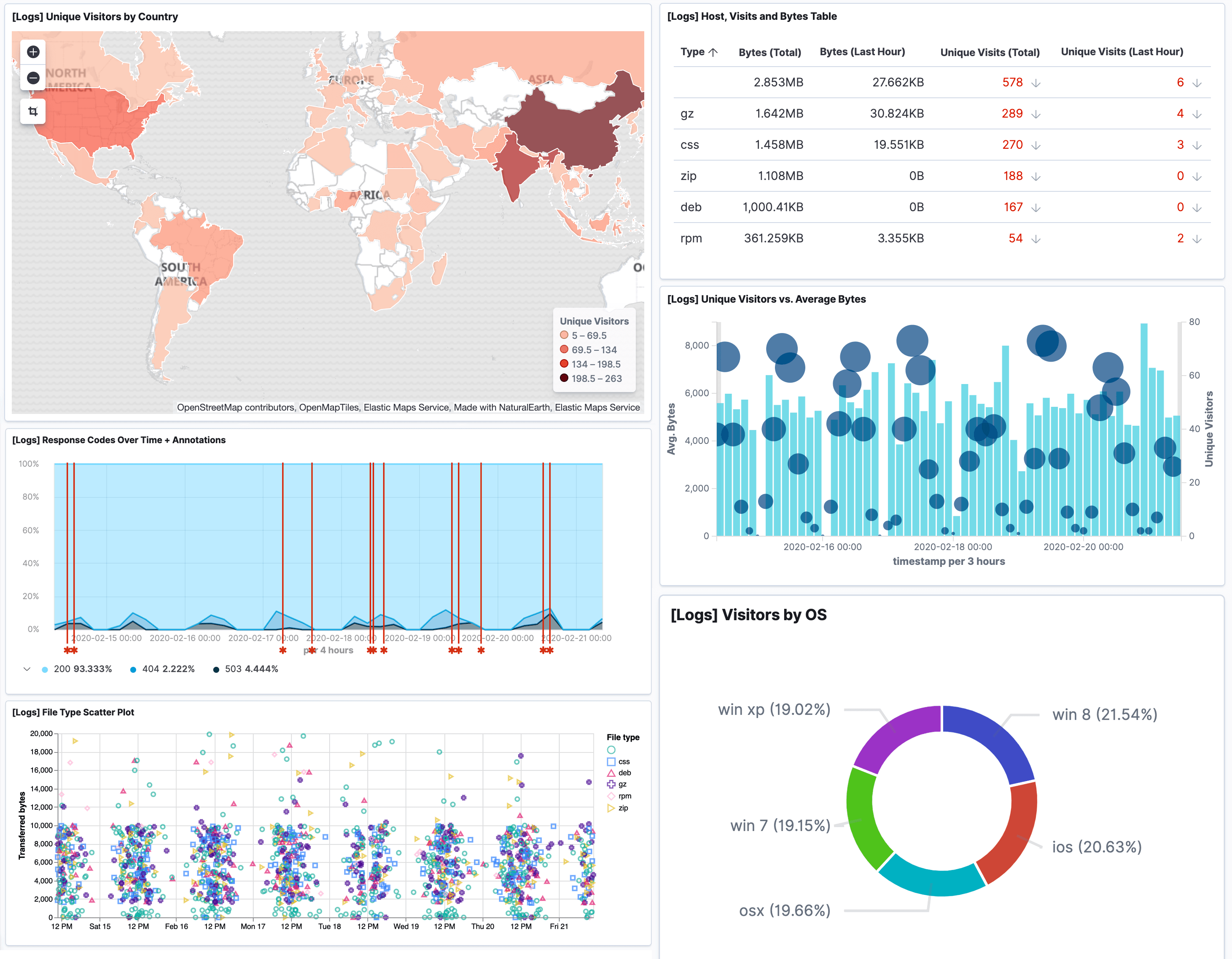
Simplify your implementation of IT compliance audits for PCI DSS, HIPAA, FISMA, GDPR, SOX, and ISO 27001. To comply with IT regulations, you can export comprehensive compliance audit reports and create custom compliance dashboards. Using Logit.io, you can also archive log data for custom time periods to meet vital log archiving requirements.
Using Logit.io you can also demonstrate compliance with more niche compliance regulations including GLBA, CCPA, and NRC. These aforementioned regulations require the retention of audit logs, a service that Logit.io provides, along with cold storage for long-term retention.