Google VPC Metrics
Ship your Google VPC Metrics via Telegraf to your Logit.io Stack
Follow the steps below to send your observability data to Logit.io
Metrics
Configure Telegraf to ship Google VPC metrics to your Logit.io stacks via Logstash.
Install Integration
Set Credentials in GCP
@intro
-
Begin by heading over to the 'Project Selector' (opens in a new tab) and select the specific project from which you wish to send metrics.
- Progress to the 'Service Account Details' screen. Here, assign a distinct name to your service account and opt for 'Create and Continue'.
- In the 'Grant This Service Account Access to Project' screen, ensure the following roles: 'Compute Viewer', 'Monitoring Viewer', and 'Cloud Asset Viewer'.
- Upon completion of the above, click 'Done'.
- Now find and select your project in the 'Service Accounts for Project' list.
- Move to the 'KEYS' section.
- Navigate through Keys > Add Key > Create New Key, and specify 'JSON' as the key type.
- Lastly, click on 'Create', and make sure to save your new key.
Now add the environment variable for the key
On the machine run:
export GOOGLE_APPLICATION_CREDENTIALS=<your-gcp-key>
Install Telegraf
This integration allows you to configure a Telegraf agent to send your metrics to Logit.io.
Choose the installation method for your operating system:
When you paste the command below into Powershell it will download the Telegraf zip file.
Once that is complete, press Enter again and the zip file will be extracted into C:\Program Files\InfluxData\telegraf\telegraf-1.34.1.
wget https://dl.influxdata.com/telegraf/releases/telegraf-1.34.1_windows_amd64.zip -UseBasicParsing -OutFile telegraf-1.34.1_windows_amd64.zip
Expand-Archive .\telegraf-1.34.1_windows_amd64.zip -DestinationPath 'C:\Program Files\InfluxData\telegraf'or in Powershell 7 use:
# Download the Telegraf ZIP file
Invoke-WebRequest -Uri "https://dl.influxdata.com/telegraf/releases/telegraf-1.34.1_windows_amd64.zip" `
-OutFile "telegraf-1.34.1_windows_amd64.zip" `
-UseBasicParsing
# Extract the contents of the ZIP file
Expand-Archive -Path ".\telegraf-1.34.1_windows_amd64.zip" `
-DestinationPath "C:\Program Files\InfluxData\telegraf"The default configuration file is location at:
C:\Program Files\InfluxData\telegraf\telegraf.conf
Configure the Telegraf input plugin
First you need to set up the input plug-in to enable Telegraf to scrape the GCP data from your hosts. This can be accomplished by incorporating the following code into your configuration file:
# Gather timeseries from Google Cloud Platform v3 monitoring API
[[inputs.stackdriver]]
## GCP Project
project = "<your-project-name>"
## Include timeseries that start with the given metric type.
metric_type_prefix_include = [
"@metric_type",
]
## Most metrics are updated no more than once per minute; it is recommended
## to override the agent level interval with a value of 1m or greater.
interval = "1m"Read more about how to configure data scraping and configuration options for Stackdriver (opens in a new tab)
Configure the output plugin
Once you have generated the configuration file, you need to set up the output plug-in to allow Telegraf to transmit your data to Logit.io in Prometheus format. This can be accomplished by incorporating the following code into your configuration file:
[[outputs.http]]
url = "https://@metricsUsername:@metricsPassword@@metrics_id-vm.logit.io:@vmAgentPort/api/v1/write"
data_format = "prometheusremotewrite"
[outputs.http.headers]
Content-Type = "application/x-protobuf"
Content-Encoding = "snappy"Start Telegraf
From the location where Telegraf was installed (C:\Program Files\InfluxData\telegraf\telegraf-1.34.1) run the program
providing the chosen configuration file as a parameter:
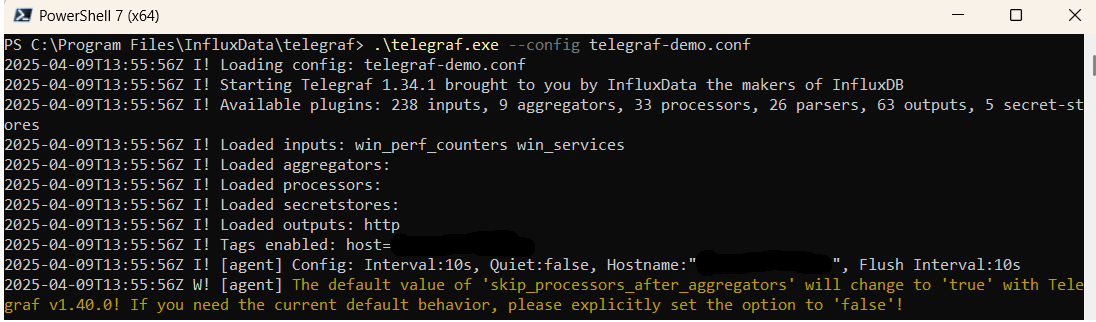
.\telegraf.exe --config telegraf.confOnce Telegraf is running you should see output similar to the following, which confirms the inputs, output and basic configuration the application has been started with:
Launch Grafana to View Your Data
Launch GrafanaHow to diagnose no data in Stack
If you don't see data appearing in your stack after following this integration, take a look at the troubleshooting guide for steps to diagnose and resolve the problem or contact our support team and we'll be happy to assist.
Telegraf Google VPC Platform metrics Overview
Telegraf, the dynamic open-source server agent by InfluxData, is designed for collecting metrics and data from a variety of sources, including cloud networks. Google VPC provides scalable and secure private networking for VMs, containers, and microservices, allowing users to customize their network topology and manage traffic flow and connectivity in a cloud environment.
By integrating Telegraf with Google VPC, organizations can monitor network performance, utilization, and security metrics in real time. This is crucial for network administrators and cloud architects who need to ensure optimal network performance, enforce security policies, and troubleshoot connectivity issues within their Google Cloud environments. Key metrics that can be monitored include network traffic flow, packet loss, latency, and the status of network security rules, providing insights necessary for maintaining a high-performing and secure cloud network infrastructure.
However, the complexity and volume of data generated by cloud networks like Google VPC can present significant challenges in terms of analysis, management, and visualization. Logit.io addresses these challenges by offering a sophisticated platform that simplifies the processing and analysis of network metrics from Telegraf and Google VPC.
With Logit.io, organizations can enhance their network monitoring and analytics capabilities, enabling them to quickly identify and address performance bottlenecks, optimize network configurations, and ensure compliance with security standards. The platform's comprehensive analytics and visualization tools support a proactive approach to network management, helping users to maintain seamless connectivity and robust security across their Google Cloud infrastructure.
For those leveraging Telegraf in conjunction with Google VPC and looking to advance their network monitoring and analytics, Logit.io provides the essential tools and support needed. Our platform facilitates the effective management of network metrics, allowing you to derive actionable insights and ensure the reliability and security of your cloud networking infrastructure. With the addition of leveraging our Google AI Platform integration, you can also automatically process and categorize logs, ensuring that the right data is sent to Logit.io for analysis. This integration enhances the accuracy and efficiency of log analysis, making it easier to identify and respond to critical events in real-time. Additionally, for a comprehensive approach to cloud security and access control, organizations can tie this data transmission process into Google Identity Access Metrics. By implementing Google Identity Access Metrics alongside Logit.io, you can monitor and assess user access and behavior patterns, strengthening your cloud security posture and ensuring that your log data is protected from unauthorized access. These integrations are perfectly in sync with Logit.io's GCP logging (opens in a new tab).